Imitation is the best form of flattery, unless it goes too far...
- Jun 10, 2018
- 2 min read
Updated: Apr 10, 2019

Now, just imagine if your voice can be duplicated (by a machine). How would anyone know that this is not YOU ? Increasingly, technology can mimic human identity and our capabilities. This can be very powerful when applied in positive ways. If you lose your voice, if you need to be in multiple places at the same time, even if you expire (die)...your memory can be preserved by your family and friends as they will be able to (always) hear your voice.
But, what happens if someone uses your synthesized voice to gain access to your private information, to your business associates, your friends, and even your family ? What harm could they do if they cannot tell it is YOU ? We are seeing an increase in power, capability, and replacement of humans by machine (intelligence, learning, and operation).
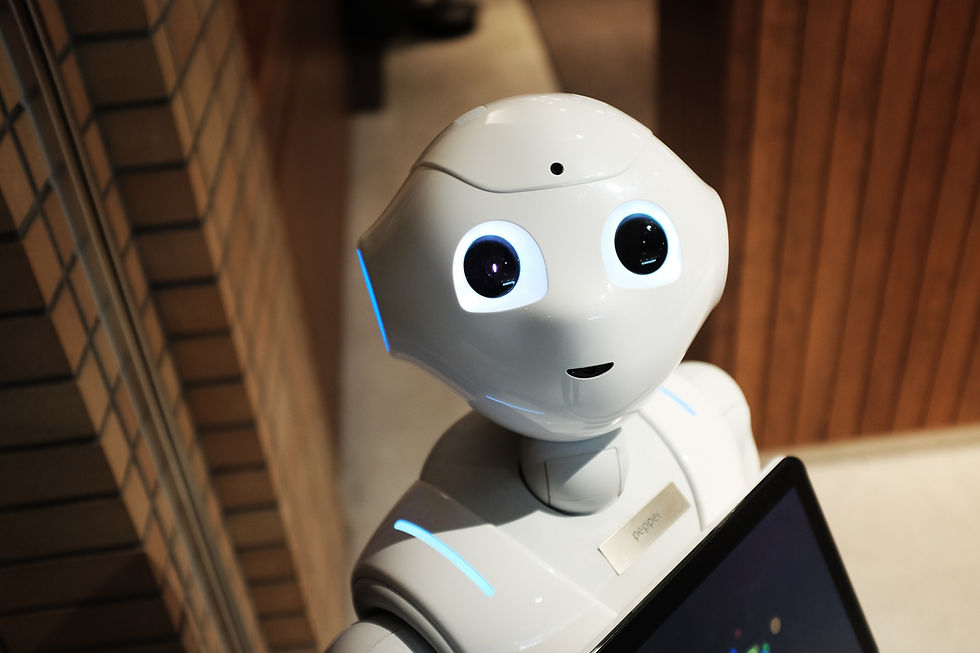
AI researchers are attempting to introduce (cute) robots to disarm our fears about AI, but we are already seeing an accelerating pace of encroachment by AI & ML in our social media, in the analysis of our behaviors and preferences for commercial opportunities, insurance companies, consumer electronics, and of course the big technology companies. AI & ML are only as good as the "designers" who have defined the algorithms, boundary points, and the problem space. If the designer is not able to foresee a scenario, then the technology may attempt to execute it's own decision paths based on it's understanding and capabilities. Most of these decisions may be harmless, but some may cause harm to a business, to a person, or beyond.
Here's a classic AI concern about it's limitation. The "Paperclip Problem" as discussed by Joshua Gans (see VOX article posted in June of this year - 2018). Being responsible and thoughtful about this new capability will be necessary at all levels of government, business, and healthcare - for starters. We may need to build an AI & ML capability to manage itself and build its own sensors and counter measures to address undesirable behaviors introduced (purposefully or by unintended consequences) to ensure the right controls are implemented with the right controls or (at least) are kept under control.




Comments